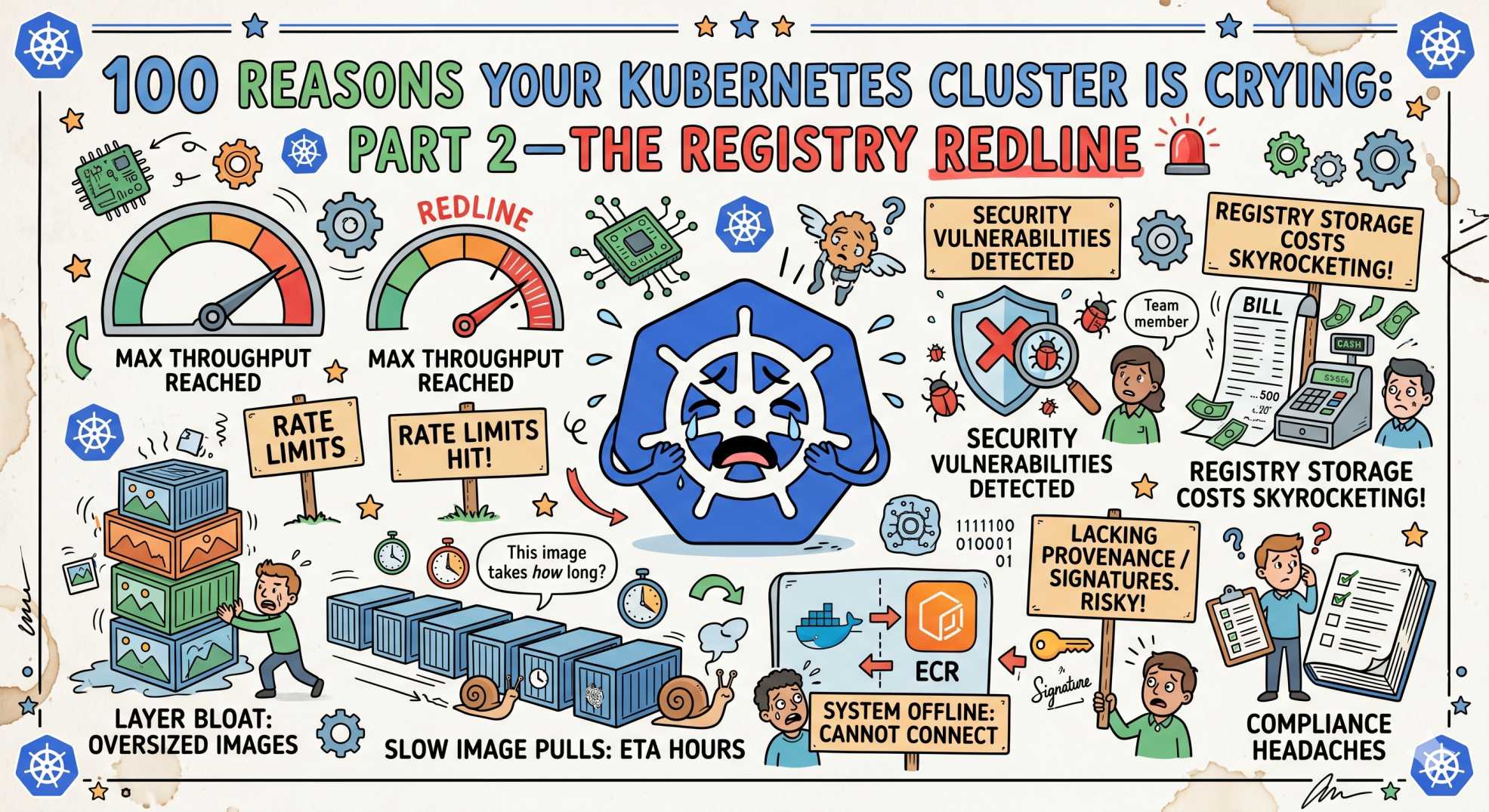
100 Reasons Your Kubernetes Cluster is Crying: Part 2-The Registry Redline 🚨
Pods not even starting? Part 2 of this Kubernetes series reveals 10 registry issues like ImagePullBackOff, auth errors, and rate limits blocking deployments.
The team at DevOps Inside knows that if your pods are the heart of your cluster, your container images are the lifeblood.
Last week, in Part 1, we looked at the Pod-pocalypse, those nasty exit codes that kill your containers after they've already started.
But what happens when your pod doesn’t even make it to the "Starting" line?
Following our From Pipelines to Prompts series, we’re moving from execution failures to the source of truth: the Registry. If your image pull fails, your deployment is just an expensive YAML placeholder.
In the world of SRE, ImagePullBackOff is the universal signal for “I’m going to be ten minutes late to this meeting.”
It’s the gatekeeper of your deployment.
Let’s break down the next 10 reasons your cluster is secretly sobbing because it can’t fetch its own code.
11. ImagePullBackOff: The Classic Waiting Room ⏳
Your pod is stuck in a loop trying and failing to fetch the image.
The SRE Reality: This is a symptom, not the root cause. Kubernetes has already failed multiple times and is now backing off.
The Fix:
kubectl describe pod <pod-name>
Check the Events section. It will tell you if it’s a 404 (Not Found) or 401 (Unauthorized).
12. ErrImagePull: The Network Hiccup 🌐
The node tried to reach the registry, but nothing responded.
The SRE Reality: Often a DNS or firewall issue, especially in restrictive VPC setups.
The Fix:
Check your egress rules. Make sure the node can actually reach the registry endpoint.
13. The ':latest' Trap: Version Roulette 🎯
You used :latest, and now environments are out of sync.
The SRE Reality: :latest is unstable and unpredictable.
The Fix:
Use semantic versioning or, better, image digests:image@sha256:...
14. ImagePullSecrets Missing: The VIP Gatekeeper 🔐
You’re pulling from a private registry without credentials.
The SRE Reality: The Secret exists, but it is not linked in the pod spec.
The Fix:
Ensure imagePullSecrets is defined and in the same namespace.
15. Private Registry Auth Timeout: Expired Credentials ⌛
Your login worked yesterday. Today it fails.
The SRE Reality: Tokens, like AWS ECR, expire frequently.
The Fix:
Use automated token refresh mechanisms or operators.
16. Manifest Unknown: Architecture Mismatch ⚙️
The image exists, but not for your node’s architecture.
The SRE Reality: ARM versus x86 mismatch.
The Fix:
Use multi-arch builds with docker buildx.
17. The 10GB Monster: Bloated Images 🧱
Your image is too large to pull quickly.
The SRE Reality: Overloaded base images and unnecessary packages.
The Fix:
Use multi-stage builds and minimal runtimes like Alpine or Distroless.
18. Insecure Registry: Protocol Clash 🚫
Your registry runs HTTP, but Kubernetes expects HTTPS.
The SRE Reality: Modern runtimes block insecure registries.
The Fix:
Whitelist it in config or use TLS.
19. Registry Rate Limiting: The Docker Hub Wall 🧱
Too many pulls from the same IP.
The SRE Reality: NAT gateway causes shared rate limits.
The Fix:
Use a local cache or mirror like Harbor or Artifactory.
20. Stale Cache: The Zombie Image 🧟
You pushed a fix, but nodes still use the old version.
The SRE Reality: imagePullPolicy: IfNotPresent prevents re-pulling.
The Fix:
Use unique tags or set imagePullPolicy: Always for development.
🤖 The AI Edge: Smart Image Optimization
In 2026, image optimization is no longer manual.
AI agents now analyze Docker layers and suggest improvements. They identify unused dependencies, reduce image size, and even generate optimized builds.
Some teams are using AI to automatically rebase images onto secure base layers without breaking compatibility.
This is moving from reactive fixes to proactive optimization.
⚡ Interactive SRE Challenge
Run this command:
kubectl get events -A --field-selector reason=Failed
Now check:
How many failures are authentication issues versus missing images?
The Verdict
The Registry is where your code meets reality.
If you treat images as immutable artifacts instead of reusable shortcuts, most ImagePull issues disappear.
🔥 What’s Next
Stay tuned for Part 3: The 'Pending Panic', where we move from the registry to the scheduler and break down why your pods get stuck in Pending and never reach a node.
💬 Quick Question: Has a registry failure ever blocked your entire deployment pipeline?
Let’s hear your worst “ImagePullBackOff at 2 AM” stories.
“You don’t own your deployment until you control your images. Everything else is just hope.”