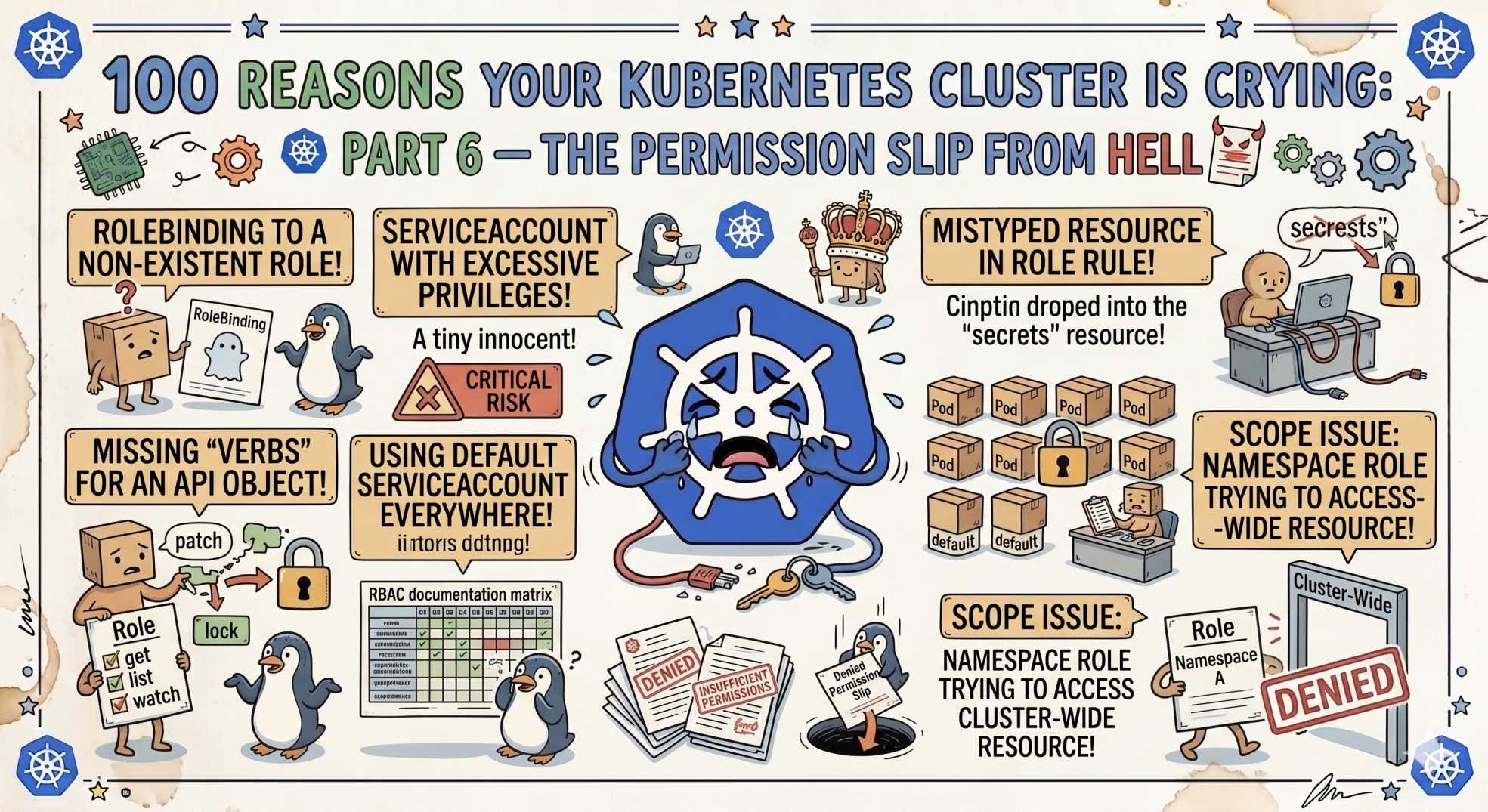
100 Reasons Your Kubernetes Cluster is Crying: Part 6- The Permission Slip from Hell
Pods failing before they even start? Part 6 reveals 10 Kubernetes security issues, from missing Secrets and RBAC denials to webhook timeouts and privileged restrictions.
The team at DevOps Inside knows that even if your networking packets are finally flowing through the "Wire," you’re still going nowhere if the bouncer at the door won’t let you in.
In Part 5, we escaped the "Networking Void", those silent packet drops that make your services invisible.
But now your traffic is reaching the pod, only to hit a "403 Forbidden" or a "Permission Denied."
Following our "From Pipelines to Prompts" series, we’re moving from the wire to the vault. If your security posture is too tight or just broken, your app is essentially in solitary confinement.
Here is Part 6: 10 reasons your cluster is sobbing over its security and RBAC.
51. User Forbidden: The Bouncer’s Denial 🚫
You try to run a simple kubectl get pods and get hit with a "Forbidden" message.
The SRE Reality:
You lack the required permission in a Role or ClusterRole.
The Fix:
Check your RoleBindings. Remember, Roles are namespaced, while ClusterRoles are cluster-wide.
52. ServiceAccount Not Found: The Identity Crisis 🪪
Your pod fails to start because it can't find its identity.
The SRE Reality:
You specified a serviceAccountName that does not exist in that namespace.
The Fix:
Run:
kubectl get sa53. Secret Not Found: The Empty Safe 🔑
The pod is stuck in CreateContainerConfigError.
The SRE Reality:
The Secret is missing or exists in another namespace.
The Fix:
Secrets are namespaced. Make sure the Secret exists in the same namespace as the pod.
54. Admission Webhook Timeout: The Slow Security Guard ⏳
Your kubectl apply hangs and then fails.
The SRE Reality:
An admission controller is not responding.
The Fix:
Check the health of your webhook or policy controller pods.
55. Forbidden Syscall: Too Much Power ⚠️
Your container crashes with "Operation not permitted."
The SRE Reality:
The app is trying to use restricted kernel operations.
The Fix:
Review your securityContext and Seccomp profile.
56. Image Signature Failure: The Forged ID 🧾
Your image is blocked before deployment.
The SRE Reality:
The cluster enforces signed images, and yours is not trusted.
The Fix:
Ensure your CI pipeline signs images correctly.
57. Invalid API Group: Speaking an Ancient Dialect 🏺
Your manifest gets rejected.
The SRE Reality:
You are using a deprecated apiVersion.
The Fix:
Update to the current supported API version.
58. HostPath Disallowed: No Touching the Host 🚷
Your pod cannot mount a host directory.
The SRE Reality:
HostPath access is blocked for security reasons.
The Fix:
Use a PersistentVolume instead.
59. The Root Lockdown: Privileged Container Blocked 🔒
Your pod is rejected immediately.
The SRE Reality:
Privileged containers are restricted.
The Fix:
Run as a non-root user and disable privilege escalation.
60. Missing TLS Secret: The Unlocked Front Door 🌐
Your app loads with a browser warning.
The SRE Reality:
TLS is configured, but the certificate Secret is missing.
The Fix:
Ensure the TLS Secret exists and is correctly referenced.
🤖 The AI Edge: Least-Privilege Modeling
In 2026, RBAC is no longer guesswork.
AI agents now analyze real usage patterns and generate least-privilege policies automatically.
Instead of over-permissioned roles, you get:
- precise access
- reduced attack surface
- minimal manual effort
This is Zero Trust that actually works.
⚡ Interactive SRE Challenge
Run:
kubectl auth can-i create pods --as system:serviceaccount:default:my-saIf it says "no", identify which Role or RoleBinding is missing.
🧠 The Verdict
Security in Kubernetes is a balance.
Too loose, and you are exposed.
Too strict, and nothing works.
The real skill is knowing where to draw the line.
🔜 What’s Next?
Stay tuned for Part 7, where we move from the Vault to the Seesaw, debugging the scaling and rollout issues that keep your deployments stuck in loops.
💬 Quick Question: What’s the most over-permissioned Role you’ve ever seen in production?
Let’s swap security horror stories in the comments.
"In Kubernetes, access is power. If everything is allowed, you’ve already lost. If nothing works, you’ve gone too far."