The Linux Files: 30 Things You Didn't Know About Linux (Part 2)
Think you know Linux? This post uncovers 30 surprising facts and hidden capabilities that even experienced users often miss.
The "Isolation Ward" – Namespaces, cGroups, and AI Guardrails
In Part 1, we learned that Linux was almost called "Freax" and that everything, even your hard drive, is just a file. But today, we’re going deeper.
If you’re running Docker or Kubernetes, you’re already using the secrets we’re about to uncover. You just might not know it yet.
For Part 2, we will be diving into the technology that allows a single Linux kernel to act like thousands of independent machines.
Here are the next 5 secrets from the engine room.
6. Containers Aren't "Real" (The Namespace Illusion) 🎭
Everyone talks about "spinning up a container." But if you look under the hood of Linux, a container doesn't actually exist as a single object. It’s an illusion created by Namespaces.
The Secret:
Namespaces wrap a global system resource in an abstraction. To a process inside a namespace, it looks like it has:
- Its own private network
- Its own users
- Even its own Process ID 1
The Senior Dev Insight:
When you run ps aux inside a container and only see two processes, but the host sees 200, you’re witnessing a PID Namespace in action.
It’s the ultimate example of controlled isolation.
7. cGroups: The Resource Police 👮
If Namespaces provide the walls (isolation), Control Groups (cGroups) provide the budget.
- The Secret: cGroups limit how much CPU, memory, or network bandwidth a process can use. Without cGroups, one "noisy neighbor" container could eat all the RAM and crash your entire node.
- Real-World DevOps Insight: This is exactly what happens when you set
resources.limitsit in your Kubernetes YAML. You aren't talking to Kubernetes; you’re asking the Linux Kernel to enforce a cGroup.
8. The "Zombie" Apocalypse 🧟
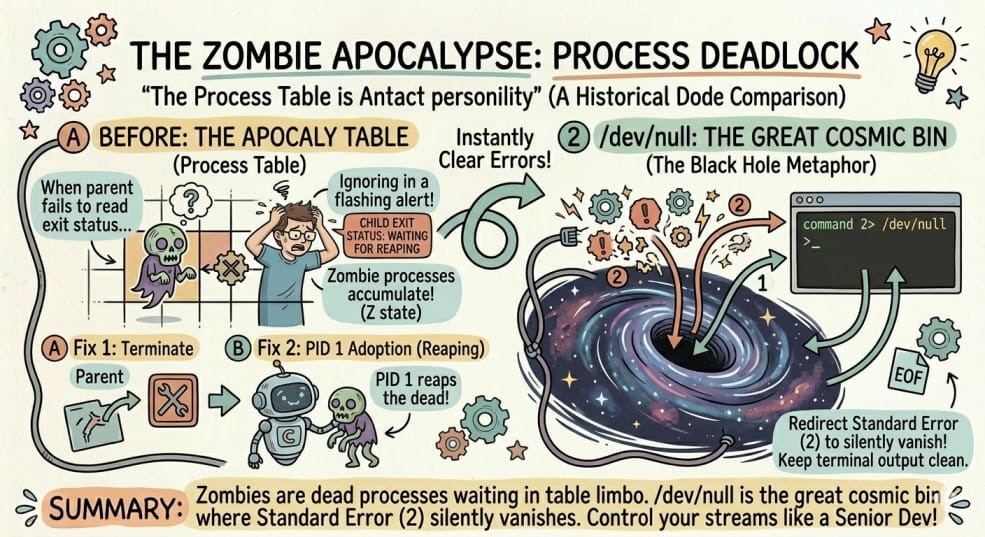
In Linux, a process can die but still remain in the process table.
These are called Zombie Processes.
- Why does it happen:
When a child process finishes execution, it waits for its parent process to collect the exit status.
If the parent process fails to do this (because it is poorly written or busy), the process stays in the Z state.
- Fix:
You cannotkill -9a zombie process because it is already dead.
The real solution is to:
- Terminate the parent process
- Or wait for the init process (PID 1) to adopt and clean it up.
9. /dev/null: The Great Cosmic Bin 🌌
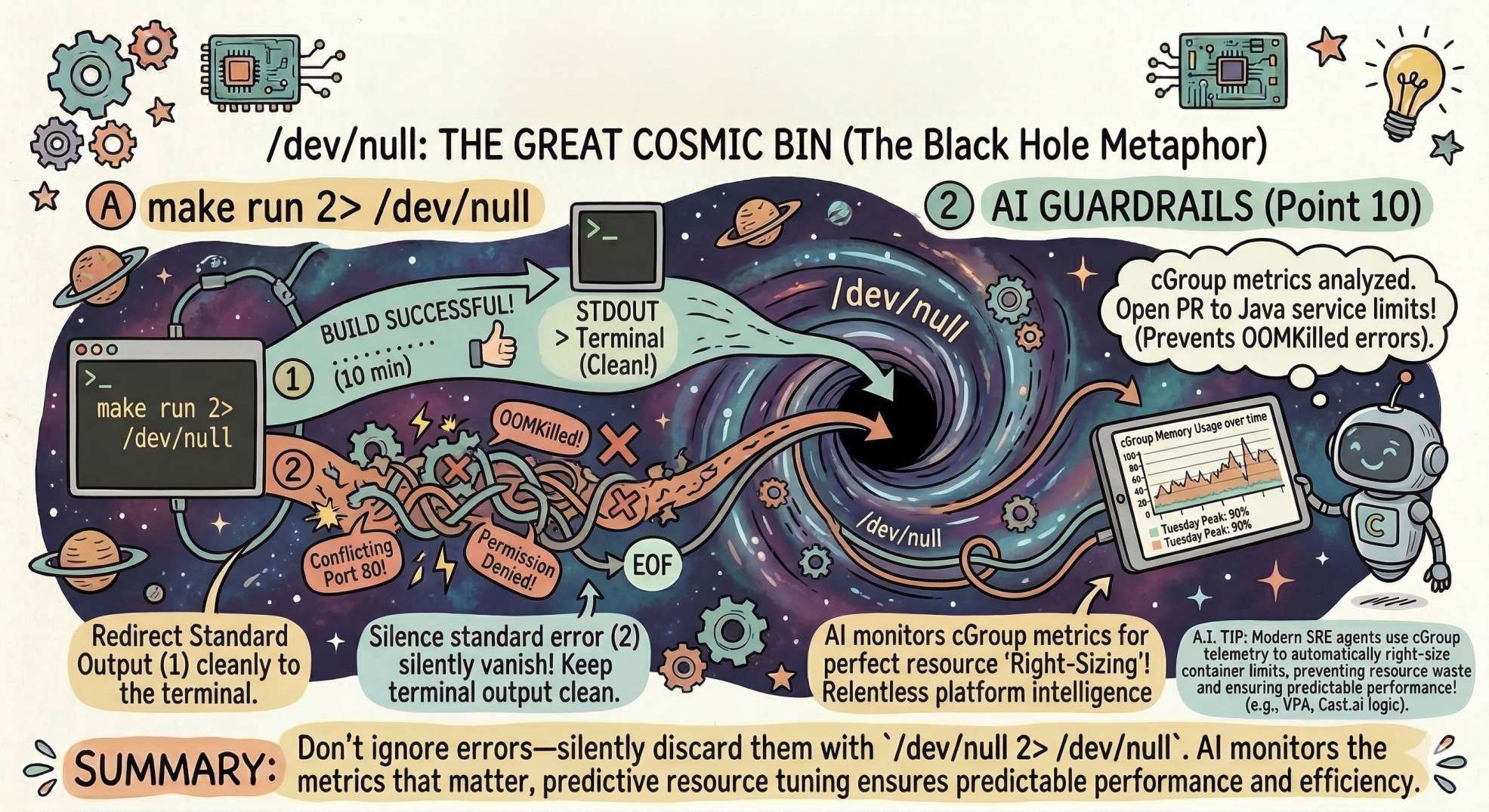
We’ve all joked about sending annoying things to /dev/null, but what is it actually?
It’s a special device file that discards anything written to it and returns EOF (End of File) when read.
In simple terms:
It is the black hole of Linux.
- The Pro Hack:
Want to run a command but ignore the error messages?
command 2> /dev/null
This redirects Standard Error (2) into /dev/null, keeping your terminal output clean.
It’s a small trick, but essential when writing clean automation scripts.
10. AI Integration: Predictable Resource "Right-Sizing" 🤖
Let’s bring in the AI layer.
One of the biggest challenges in Platform Engineering is deciding how much CPU or RAM a container actually needs.
Enter tools like:
- Vertical Pod Autoscaler (VPA)
- Cast.ai
- Other AI-driven optimization platforms
The Real Concept: These tools analyze cGroup resource usage over time.
Instead of guessing "2 GB RAM should be enough," the AI observes the real behavior of the application and adjusts resource limits accordingly.
This helps prevent issues like OOMKilled errors.
The Bridge: Clawd-Bot doesn't just watch logs; it watches cGroup metrics.
It might say:
"Your Java service peaks at 90% memory every Tuesday at 10 AM.
Let's adjust the limits and open a pull request."
Now that’s platform intelligence in action.
Looking Ahead to Part 3: Next, we move from process isolation to networking and security.
We’ll explore:
- The "Shadow Network" (eBPF)
- Hidden networking layers in containers
- How AI-driven monitoring can detect suspicious activity before attackers even finish running their first
whoami.
💬 Quick Question: Have you ever encountered a Zombie process in production? How did you track it down and resolve it?
Share your experience in the comments!
"Namespaces are the walls, cGroups are the budget, and AI is the auditor.
In the world of containers, Linux is the landlord who never sleeps."